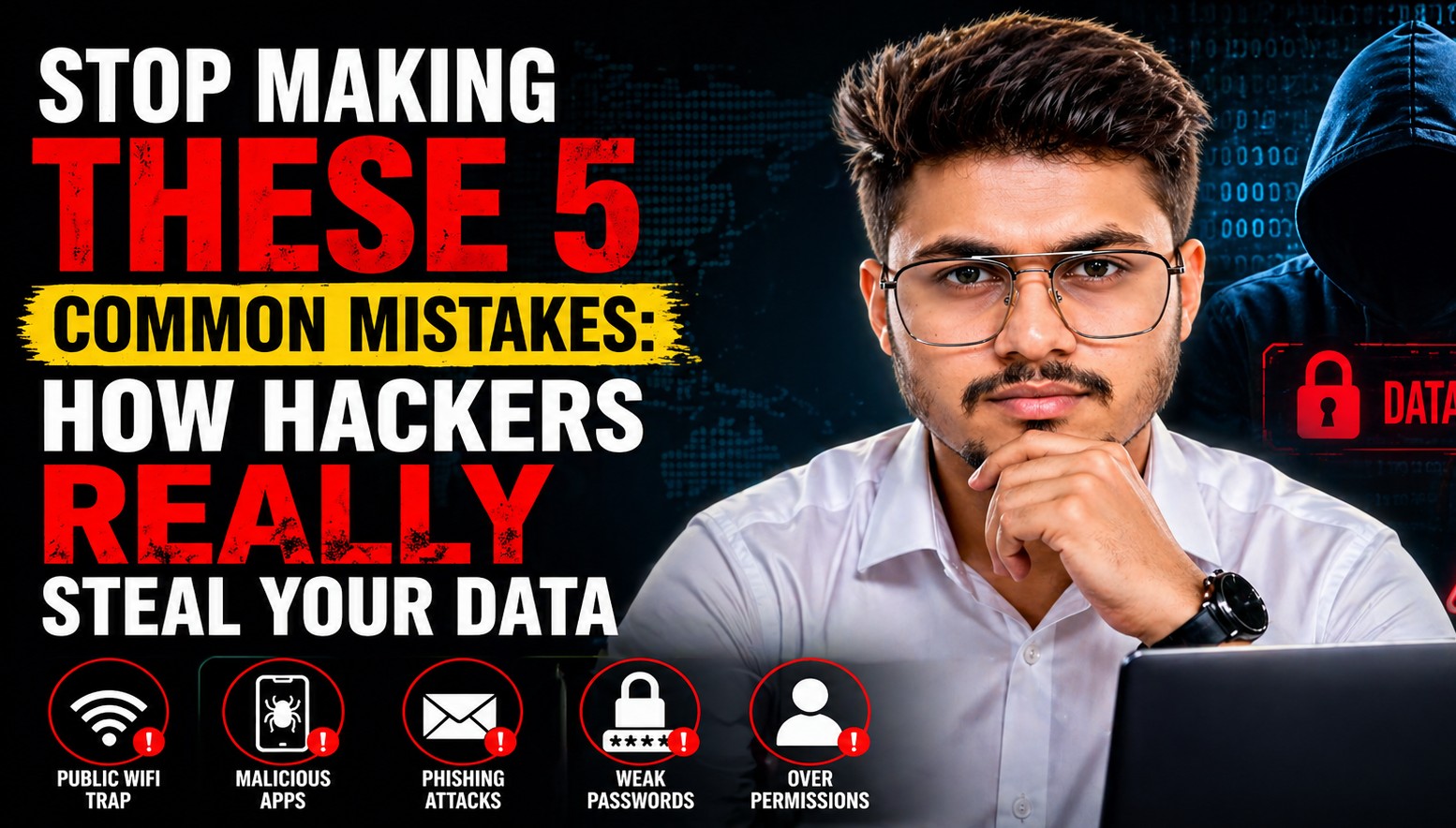
Stop Making These 5 Common Mistakes: How Hackers Really Steal Your Data
most people believe that hackers are “digital wizards” who use complex code to break through high-tech firewalls. While sophisticated attacks do exist, the reality is much simpler – and scarier. Most cybercriminals don’t “break in”; they are “let in” through small, everyday human errors. If you think your data is safe just because you have…