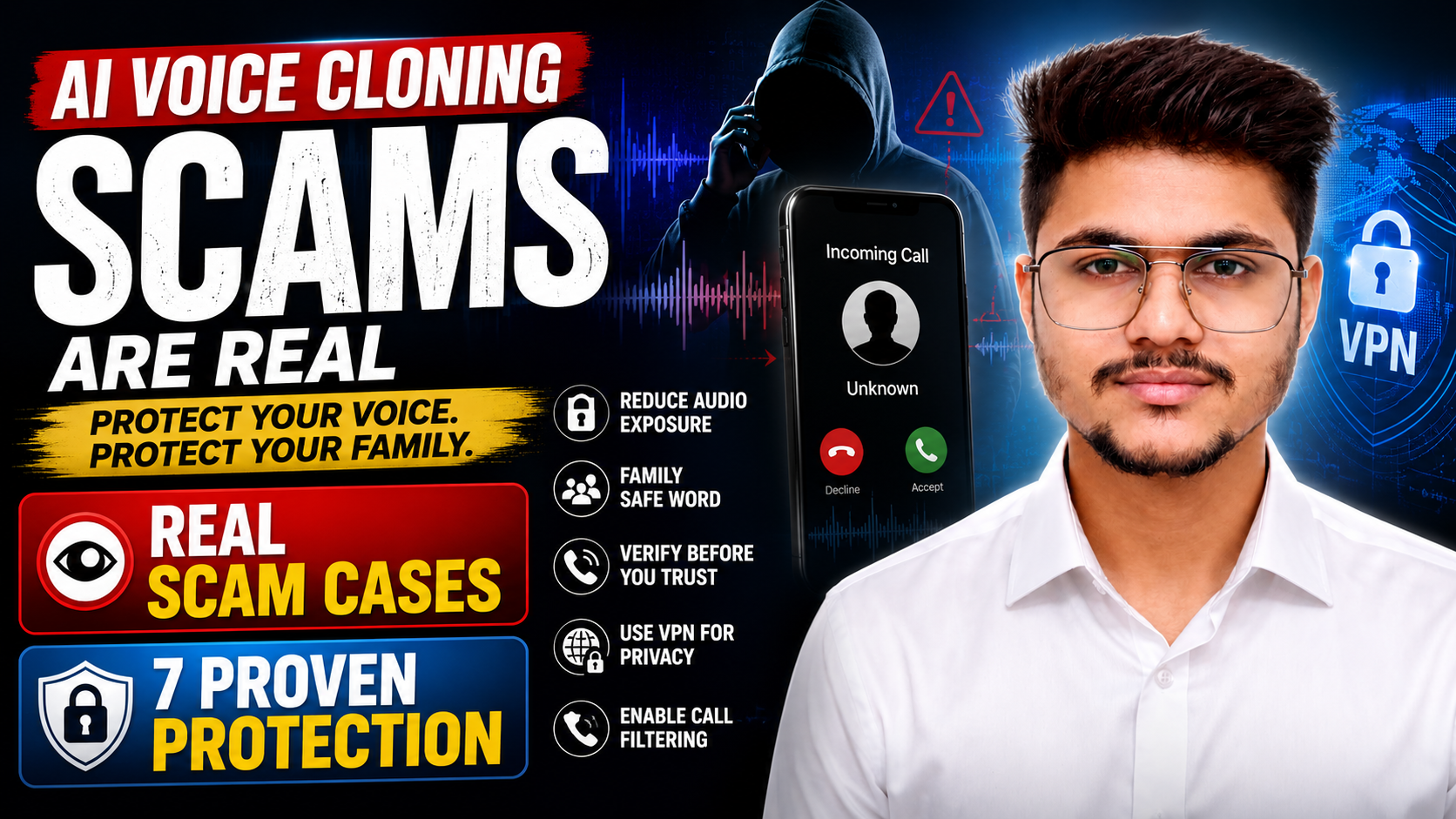
Protecting Your Identity from AI Voice Cloning Scams
AI voice cloning has moved from a research curiosity to an active criminal tool. Scammers can now replicate any person’s voice using a short audio sample pulled from a social media video or voice note – and use it to defraud their family members, colleagues, or employers over the phone. The technology is widely accessible,…