Is it okay to visit the dark web without a VPN?

People commonly wonder whether VPN access is necessary when visiting the Dark Web. The internet hides an intentionally hidden portion named the dark web which search engines cannot locate.
The dark web runs different websites and platforms which create an anonymous user experience because of their distinct network design. Any illegal activities conducted on the dark web remain unlawful actions that lead to serious legal penalties.
Layers of the Internet
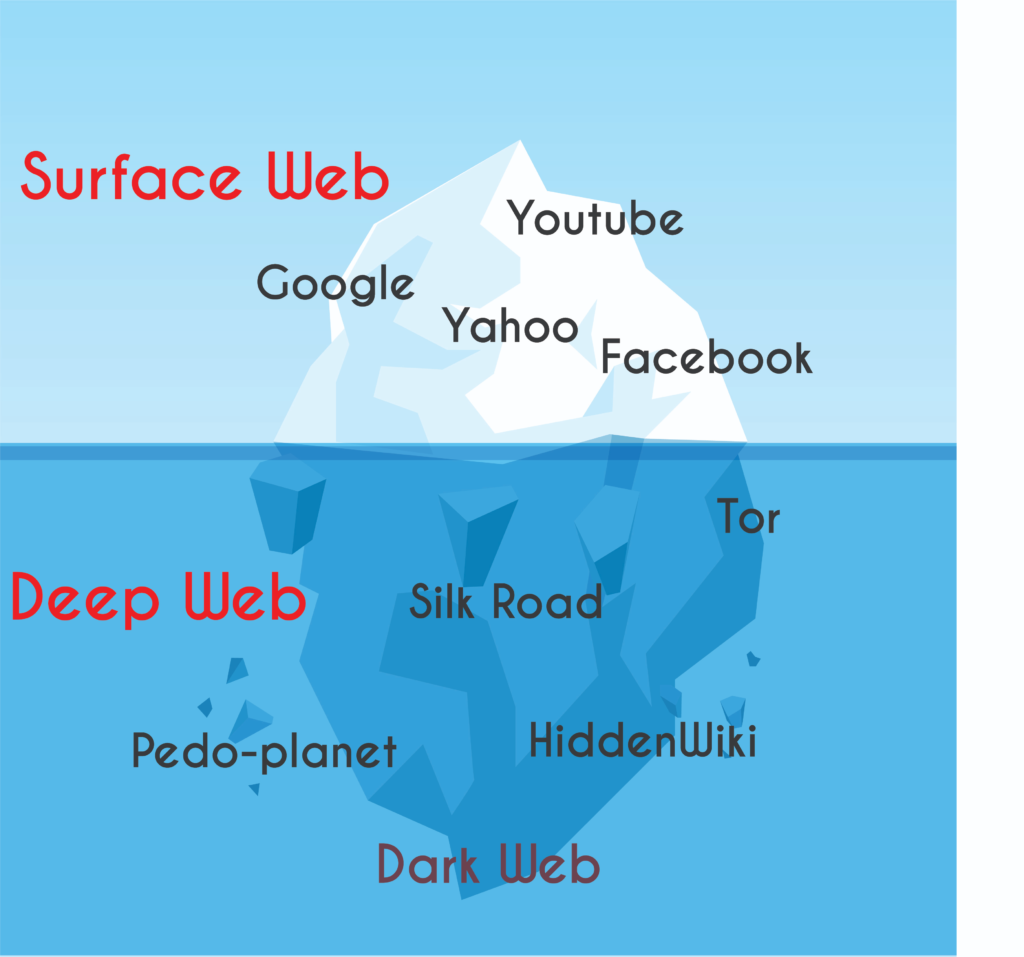
- Surface Web: All websites registered for search engine indexing reside within this layer including those hosted by Google and other major search engines. The layer includes all internet pages ranging from news websites to social media networks and online shopping sites.
- Deep Web: The deep web represents the large section of internet data that search engines cannot access for indexing. Internet users access the deep web through private databases as well as password-protected websites and several other concealed web pages. Law abiding activities exist throughout the deep web exactly because its anonymous content structure creates misunderstandings for people.
- Dark Web: A specialized anonymity system called the dark web operates beneath the deep web by hiding from standard web tools and tools for browsing. Users need specific software like Tor (The Onion Router) to access the dark web because this tool allows them anonymous browsing capabilities. Anonymity together with privacy stand as the primary purpose of the dark web which does not exist on the surface web. Users experience privacy through encryption-enabled and routing-based processes that create difficulties for observing their activities.
Using a VPN for Dark Web Access
Use a Secure Connection: Your dark web connections should use only secure and private networks. A Virtual Private Network (VPN) provides secure internet traffic encryption together with IP address anonymity. The addition of a VPN delivers added anonymity which hinders others from tracking your dark web activity to your actual identity.
What Is the Dark Web?
Search engines cannot access the hidden internet section which operators name the dark web. Users find anonymity through hidden websites and platforms that make up the dark web because these elements run separately from ordinary search engine-accessed pages. This explanation includes six important details about the subject matter.
- Legality: The worldwide access to the dark web remains lawful throughout most nations of the world. Environment agencies in the U.S. along with the U.K. and several European nations do not prohibit dark web browsing activities. Governments in countries with rigorous internet control systems including China and Russia along with Iran often ban access to the dark web services because they do not approve of these operations.
- Size and Navigation: The dark web exists as a smaller domain than the surface web pages do. The dark web comprises only a minor segment of the deep web because it remains distinct from the much larger deep web contents. People encounter difficulty when accessing this area because of its planned hidden nature.
- Anonymity: The dark web offers anonymity yet remains one option instead of being the sole method to maintain online anonymity. Users can find access methods to the dark web through different approaches that exist either within the dark web or outside of it. Tor (The Onion Router) serves as a common tool to reach the dark web yet it provides privacy protection which still has vulnerabilities.
- Cryptocurrencies: Despite criminal use of cryptocurrencies for secrecy illegitimate transactions criminals use these digital currencies for multiple legitimate reasons that extend past dark web activities.
- Criminal Activity: Even though criminalities exist on the dark web we need to understand that illegal operations take place throughout the surface web. The dark web exists beyond criminal domains since normal users can access its numerous legal functions.
Risks of Accessing the Dark Web Without a VPN
1. Security Threats
- Exposure to Malicious Content: Various websites on the dark web host dangerous content that includes risky elements such as malware together with phishing attacks and forbidden marketplaces. Your connection remains at risk when unprotected because an interception attack can threaten your device together with access to your personal information.
- Unencrypted Traffic: Your dark web connection stays unencrypted when you navigate without a VPN protection. Your connection remains exposed for surveillance by third parties including hackers and government agencies to access sensitive data including login information and financial information and personal messages.
2. Legal Implications
- Unintentional Illegal Activity: Accessing the dark web without appropriate safeguards exposes users to illegal activities despite its legal and illegal content. Any unintentional discovery of illegal marketplaces and forums through the dark web might result in legal repercussions.
- Country-Specific Laws: Dark web access regulations differ among different nations due to their own legal standards. Access to dark web websites remains legal at a national level in some countries although other counties consider it a punishable offense. Your IP address will be visible without using a VPN thus exposing your online activities to authorities for tracking.
3. Privacy Concerns
- IP Address Exposure: Your actual IP address becomes visible to others when you access the dark web without activating a VPN. Your online privacy becomes compromised when you connect without a VPN that enables others to view your current online locations.
- ISP Monitoring: Internet Service Providers maintain the ability to track each user’s Internet activities. Using a VPN protects your dark web activity from view because your Internet Service Provider would remain unaware of your internet activities without VPN encryption.
Using a VPN for Dark Web Access
To mitigate these risks, consider using a reliable VPN when exploring the dark web:
- Encrypt Your Traffic: The encryption provided by VPN protects your internet traffic so that unauthorized viewers cannot understand the information sent through the network. A VPN functions through two security functions: it ensures privacy of your IP address and implements encryption to protect your data.
- Choose a Reputable VPN: Select astable and reputable VPN provider that maintains a strict no-logging policy in its services. Choose a VPN service which offers robust encryption together with an extensive server network and straightforward applications.
How a VPN Enhances Security on the Dark Web
1. IP Address Masking
- What Is an IP Address?: Internet Protocol addresses works as unique numerical identifiers which connect each device to the online network. The identification function of an IP address makes possible the transfer of data between different devices.
- Masking Your IP Address: The dark web link up with a VPN helps you conceal your genuine IP address from view. The VPN system provides you with an alternative IP address that comes from its server infrastructure. A VPN service conceals your genuine location information so others cannot identify your activities on the internet.
2. Data Encryption
- Securing Your Traffic: A VPN uses strong encryption protocols to create secure transmission through the internet. The data pathway between your device and VPN server is encrypted in a way that produces unreadable information for anyone attempting to intercept it.
- Protection Against Interception: Internet traffic becomes accessible to hackers and government entities because encryption systems are not applied in this case. The encryption technique enables data interception to remain indecipherable to unauthorized persons unless they possess the encryption key.
3. Anonymity Benefits
- Anonymizing Your Online Presence: Waiving a VPN service will grant you further anonymity protection. Internet service providers along with other entities lose their ability to monitor your online activities because the VPN creates an encryption between your device and the VPN server. Your device establishes encrypted internet communication toward the VPN server without anyone else able to track it.
- Avoiding ISP Monitoring: The practice of tracking user browsing activities becomes possible through the operations of Internet Service Providers. The use of a VPN blocks your ISP from monitoring your online activity since it hides your visited websites from their view.
Consequences of Not Using a VPN on the Dark Web

1. Increased Vulnerability to Cyber Attacks
- Malware and Phishing: Internet traffic without VPN security becomes accessible to competitors. The existence of this security vulnerability allows you to become exposed to harmful internet content such as malware attacks and phishing attempts. Your device becomes vulnerable because cybercriminals find ways to exploit security weaknesses through their attacks.
- Man-in-the-Middle Attacks: Attackers can intercept data because your connection operates without encryption. A middle-man attacker intercepts your communications to both eavesdrop and steal sensitive information as well as introduce dangerous code.
2. Government Surveillance
- IP Address Tracing: Users who access the dark web without VPN protection reveal their original IP address. Your activities on the dark web are monitorable through the visible IP address by both government agencies and law enforcement departments. The content you view together with your location might result in legal problems due to IP address monitoring.
- Privacy Erosion: Government surveillance actively interferes with your private right to personal information. Neither illegal nor legal online activities can protect you from surveillance that monitoring authorities might conduct.
3. Tracking by Malicious Entities
- Dark Web Threats: The dark web hosts various websites, some of which harbor illegal content. Your connection remains exposed to tracking by bad actors if you do not use a VPN. The potential threats to your connection include cybercriminals, hackers, as well as persons with ill intent.
- Unencrypted Traffic: Internet communications that lack encryption provide access to personal information about what users browse online and what interests them along with their security weaknesses. This information allows hackers to take advantage of it.
Safer Alternatives to VPN for Dark Web Access
Tor Network (The Onion Router):
- Overview: The open-source Tor software operates free of charge to provide users with anonymous internet communication pathways. The software guides your Internet traffic into passing through multiple servers that pass your IP address onto different nodes operated by volunteers.
- How It Works: Your data travels across several Tor nodes creating strong hurdles preventing anyone from tracking your internet use. Tor provides security but users must know that it contains various potential weaknesses.
- Pros: High level of anonymity, easy to use, community-driven.
- Cons: Slower browsing speeds, potential exit node risks.
- Recommendation: If anonymity is your top priority, Tor is an excellent choice.
Proxy Servers:
- Overview: Proxy servers act as intermediaries between your device and the websites you visit. They can hide your IP address and provide limited anonymity.
- Types of Proxies:
- HTTP/HTTPS Proxies: These work for web browsing and are suitable for accessing the dark web.
- SOCKS Proxies: More versatile and can handle various types of traffic.
- Pros: Faster than Tor, simple setup.
- Cons: Limited security, potential risks if using untrustworthy proxies
- Recommendation: Use reputable proxy services and be cautious.
Secure Browsers:
- Overview: Some web browsers prioritize privacy and security features. While they don’t replace a VPN, they enhance your protection.
- Examples:
- Brave: Blocks ads and trackers, offers private browsing mode.
- Firefox: Supports various privacy extensions and configurations.
- Tor Browser: Based on Firefox, specifically designed for accessing the dark web.
- Pros: Improved privacy, user-friendly.
- Cons: Not a complete substitute for a VPN.
- Recommendation: Use a secure browser alongside other privacy tools.
Best Practices for Dark Web Browsing
1. Combining VPN with Tor
- Why Combine Them?: Using both a Virtual Private Network (VPN) and the Tor network provides an extra layer of security and anonymity.
- How It Works:
- Step 1: VPN Connection: Start by connecting to a reputable VPN. This encrypts your internet traffic and masks your IP address.
- Step 2: Tor Browser: Open the Tor Browser, which routes your traffic through a series of volunteer-operated servers (nodes). This conceals your identity and location.
- Step 3: Dark Web Access: With the combined setup, you can access the dark web while benefiting from both VPN encryption and Tor’s anonymity.
2. Using Secure and Updated Software
- Keep Everything Updated: Keep your operating system along with browser and security software programs up to date. Updates contain solutions that fix security holes which possible attackers could take advantage of.
- Secure Browsers: Brave and Firefox with privacy extensions together with the Tor Browser provide excellent choices for private browsing. These browsers position privacy and security features ahead of all other functionalities.
3. Staying Anonymous and Safe
- Avoid Personal Information: Never share personal details or use real names on the dark web. Assume that any information you provide could be used against you.
- Be Skeptical: Exercise caution when interacting with unknown websites or individuals. Verify sources and avoid suspicious links.
- Legal Boundaries: Understand the legal implications of your actions. While not all dark web activity is illegal, some actions may violate local laws.
- Limit Downloads: Avoid downloading files unless necessary. Malicious files can compromise your device.
- Exit Nodes: Be aware that the last node in the Tor network (exit node) can potentially see your unencrypted traffic. Use HTTPS whenever possible.
Understanding Legal Boundaries
- Legal Varies by Country: Countries maintain varied legislation about access to the dark web. The process of accessing dark web platforms remains lawful in various locations although participating in illegal acts while using this network remains unlawful. You must comprehend every regulation that applies to your location.
- Illegal Activities: The dark web hosts both legal and illegal content. Participating in illegal conducts involving drug purchases as well as weapon or data theft deals can lead to serious legal repercussions. Anonymity provides no protection from prosecution under the law.
- Gray Areas: The dark web hosts services which merge between legality and illegality. Journalists who do whistleblower work and other sensitive information sharers use the dark web as a platform. Legal boundaries remain unclear even when dealing with activities located on this platform.
Ethical Use of the Dark Web
- Purpose Matters: Consider your intentions. You explore places for curiosity reasons or conduct research while also aiming for anonymity. People who follow ethical computing standards need to protect the wellbeing of others while safeguarding personal information.
- Avoid Illegal Activities: Stay away from illicit marketplaces and illicit child material as well as destructive content. Respect ethical standards in every environment where you maintain anonymity.
- Privacy and Anonymity: You can achieve private activities through the dark web but this privilege does not authorize unethical conduct. Users should exercise responsible use of anonymity by recognizing and upholding the rights of others.
This analysis of the dark web and its key points ends here before we turn to future insight into using a VPN for dark web access. This piece will explore end thoughts regarding dark web access with a VPN and summarize all previously mentioned points.
Important Key Points
- Understanding the Dark Web:
- The dark web is intentionally hidden from traditional search engines and operates within a network of websites that offer anonymity.
- It’s a subset of the deep web, accessible through specialized software like Tor.
- While not all dark web activity is illegal, it’s essential to approach it with caution.
- Risks of Accessing the Dark Web Without a VPN:
- Security threats include exposure to malicious content and unencrypted traffic.
- Legal implications vary by country, and unintentional illegal activity can occur.
- Privacy concerns arise due to IP address exposure and ISP monitoring.
- How a VPN Enhances Security on the Dark Web:
- A VPN masks your IP address, encrypts your traffic, and provides anonymity.
- Combining a VPN with Tor offers even greater security.
- Safer Alternatives to VPN for Dark Web Access:
- Consider Tor, proxy servers, or secure browsers.
- Each option has its pros and cons, so choose based on your needs.
- Legal and Ethical Considerations:
- Laws regarding the dark web vary by country.
- Ethical use involves avoiding illegal activities and respecting privacy.
Is It Okay to Visit the Dark Web Without a VPN? My Final Opinion
Visiting dark web requires a VPN because it is inadvisable to browse this area without this security tool. If you do not use VPN when accessing the dark web you will face severe security, privacy and legal vulnerabilities.
Your IP address along with your online activities becomes accessible to cybercriminals and more when you do not use VPN services. You can maintain secure browsing by using a VPN which conceals your IP address through encryption to provide privacy thereby protecting your activities online. Users should protect themselves by combining Tor with a VPN for total dark web security.
Loading newsletter form...






