Stop Making These 5 Common Mistakes: How Hackers Really Steal Your Data
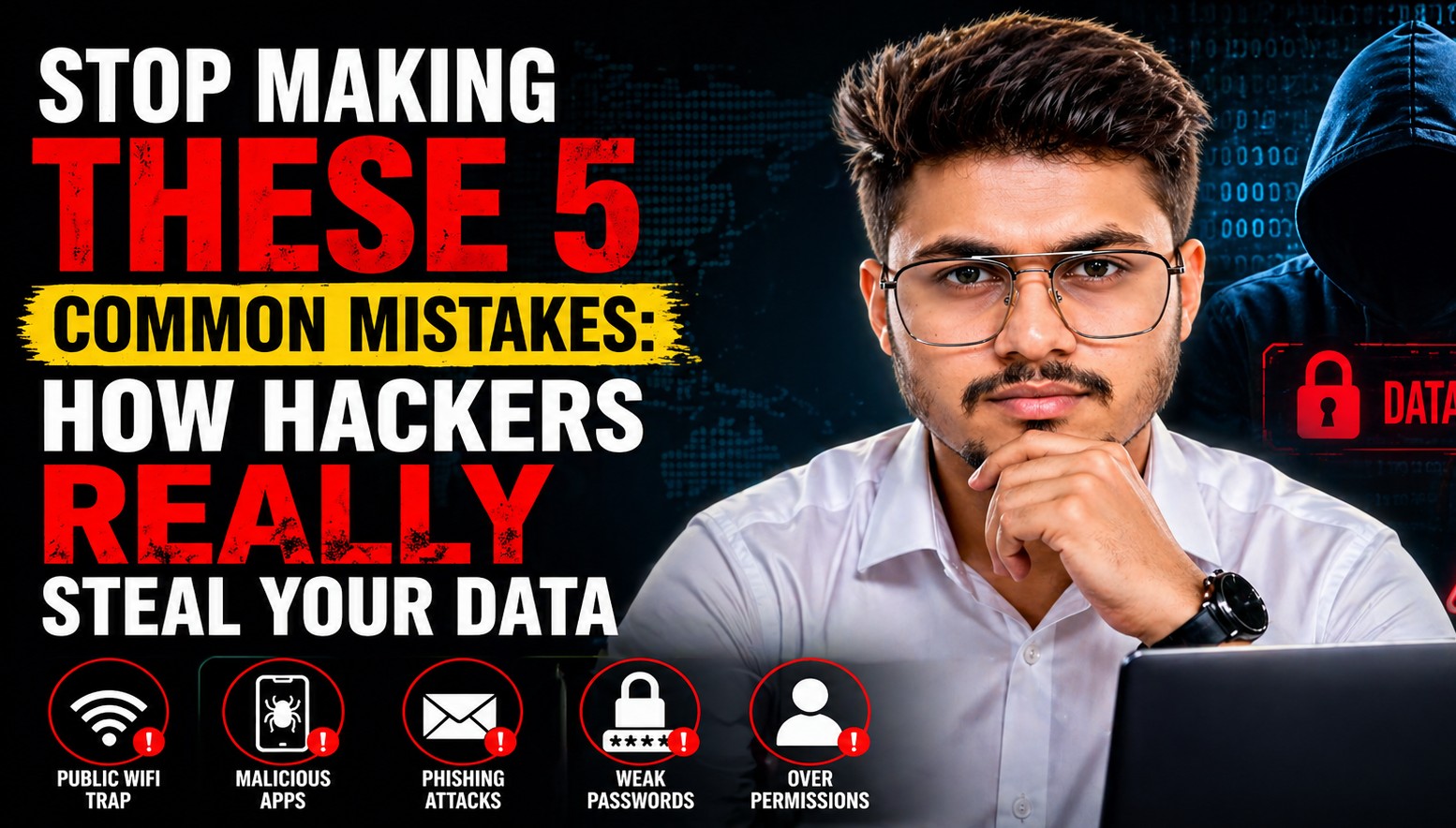
most people believe that hackers are “digital wizards” who use complex code to break through high-tech firewalls. While sophisticated attacks do exist, the reality is much simpler – and scarier. Most cybercriminals don’t “break in”; they are “let in” through small, everyday human errors.
If you think your data is safe just because you have a password, you are missing the bigger picture. In this guide, we will dive deep into the five most common security loopholes hackers exploit and provide a roadmap to secure your digital life.
1. The Public WiFi Trap: Convenience vs. Security
We’ve all been there – sitting in a cafe or waiting at an airport, connecting to the “Free Guest WiFi.” While convenient, these networks are often completely unencrypted.
- How the Hack Works: Hackers can perform a “Man-in-the-Middle” (MitM) attack. They position themselves between you and the connection point. Everything you do – typing a password, checking your bank balance, or sending a private email – passes through their eyes first.
- The Fix: Never conduct sensitive business on public networks. If you must use them, always use a reputable VPN (Virtual Private Network) to encrypt your data.
2. Malicious Apps: The Trojan Horses in Your Pocket
Not every app on the internet is what it claims to be. Many users download “Modded” or “Premium for Free” versions of popular apps from third-party websites.
- How the Hack Works: These apps often contain “Spyware” or “Keyloggers.” Once installed, they can record your screen, access your camera, and even intercept your SMS messages to steal OTPs (One-Time Passwords).
- The Fix: Stick to the official stores like the Google Play Store or Apple App Store. Even then, check the developer’s reputation and read the reviews before hitting download.
3. Phishing: The Art of Digital Deception
Phishing is the most common way hackers steal credentials. It starts with a sense of urgency: an email saying your account is suspended, or a WhatsApp message claiming you’ve won a massive prize.
- How the Hack Works: These messages contain a link to a fake website that looks exactly like your bank or social media login page. When you enter your details, you aren’t logging in; you are handing your credentials directly to a criminal.
- The Fix: Always inspect the URL. If it says
secure-bank-login.netinstead ofbankname.com, it’s a scam. Remember: No legitimate institution will ask for sensitive info via a random link.
4. The Weakest Link: Predictable Passwords
If your password is your pet’s name, your birthday, or “Password123,” you are an easy target. Hackers use “Brute Force” attacks – software that can try millions of common combinations in minutes.
- The Fix: Use a Password Manager (like Bitwarden or Dashlane) to generate unique, complex passwords for every account. Most importantly, enable Two-Factor Authentication (2FA). This ensures that even if a hacker knows your password, they can’t get in without the secondary code on your phone.
5. Over-Permission: Why Does a Flashlight Need Your Contacts?
When you install an app, it asks for “Permissions.” Most of us click “Allow” without thinking. This is a massive privacy leak.
- How the Hack Works: If a basic utility app has access to your microphone, location, and contacts, it can track your movement and listen to your conversations for data mining or more malicious purposes.
- The Fix: Go to your phone settings and conduct a Permission Audit. Revoke any access that doesn’t seem necessary for the app’s primary function.
Your 5-Minute Security Checklist
To make sure you are fully protected, do these three things right now:
- Check for Updates: Ensure your phone’s OS and all apps are updated to the latest version to patch security holes.
- Enable 2FA: Turn on Two-Factor Authentication on your Google, Facebook, and Banking accounts.
- Delete Unused Apps: If you haven’t used an app in three months, delete it. It’s one less door for a hacker to try.
Final Thoughts
Cybersecurity is not a one-time setup; it’s a habit. By staying alert and being skeptical of “free” offers or urgent messages, you can stay ahead of 99% of hackers. Don’t wait for a breach to happen – secure your data today.
Loading newsletter form...